ARTICLE AD BOX
Ever since the commercial internet began to reach mainstream users, porn sites have been used to carry malware. The latest trend: Russian hackers are using AI-driven “deepnude generators”—applications that create nude images from user-uploaded pictures—to infect the stupidly horny.
Worst of all, the hackers appear to be connected to FIN7, a notorious cybercrime group active since 2012. Last year, the U.S. Department of Justice pronounced the gang dead following the arrest, conviction, and jailing of three members, including FIN7’s alleged “manager,” a Ukrainian national named Fedir Hladyr. The hacker group was believed to have caused $3 billion in damage worldwide.
“FIN7 as an entity is no more,” U.S. Attorney Nick Brown said in May 2023.
Apparently, he spoke too soon.
Last week, Virginia-based security company Silent Push published a report claiming that the group is back—and worse than ever. Silent Push reported that FIN7 has recently set up some 4,000 fake domains and subdomains, including at least seven “deepnude generator” websites described as “honeypots of malware.”
“FIN7 AI deepfake honeypots redirect unsuspecting users who click on the ‘free download’ offer to a new domain featuring a Dropbox link or another source hosting a malicious payload,” the Silent Push report said, noting that all of the sites have since been taken down. However, they "believe it’s likely new sites will be launched that follow similar patterns.”
The websites included names like easynude(.)website, ai-nude(.)cloud, and nude-ai(.)pro.
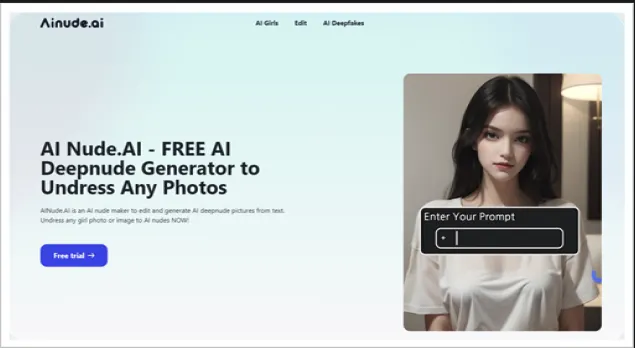 Image: Silent Push
Image: Silent PushDetecting malware attacks is challenging, San Jose State University College of Engineering Professor Ahmed Banafa told Decrypt. Malware downloads happen quickly after the user interacts with the website. Shutting down these websites becomes a game of whack-a-mole; when one website is shut down, others quickly replace it.
“It's just changing the domain, and the code is the same,” Banafa said. “Even if you confiscate the server farms in a different country, it's very easy to get it done again.”
Porn sites are a common attack vector, he said. “This is the weakest point—the weakest point of the network is the human," he explained.
While the AI twist is new, the broader trend definitely isn't. In late March 1999, a computer programmer named David Lee Smith used a hijacked America Online account to spread the “Melissa” virus via an internet newsgroup called “alt.sex.” Once downloaded, the malware—which cost an estimated $80 million to clean up—took over the user’s PC and sent infected emails to the victim’s contacts.
In the early 2000s, cybercriminals began using adult websites to distribute Trojan horses and spyware disguised as video players or codecs. These programs, like the ILOVEYOU virus, recorded keystrokes and changed browser settings without the user’s knowledge.
Last month, the city of San Francisco filed a lawsuit against 18 illegal deepfake websites and apps that offered to undress or “nudify” women and girls. Collectively, the lawsuit said, the sites have been visited over 200 million times in the first six months of 2024.
“This investigation has taken us to the darkest corners of the internet, and I am absolutely horrified for the women and girls who have had to endure this exploitation,” San Francisco City Attorney David Chiu said at the time. “Generative AI has enormous promise, but as with all new technologies, there are unintended consequences and criminals seeking to exploit the new technology.”
FIN7 is the name security researchers gave the group when it was first identified, and it stands for Financially Motivated Threat Group 7. The hackers refer to their group by many different names, including Carbanak or the Navigator Group.
It’s believed to be tied to Russia based on the fact that it recruits Russian speakers and targets mostly U.S. and European corporate users as a way to infiltrate their work systems. Likewise, Russia itself has been largely uncooperative in helping catch the perpetrators, according to law enforcement officials.
FIN7’s shenanigans have gone far beyond porn sites. Security experts believe the group has stolen millions by infiltrating point-of-sale systems in the hospitality and food industries to steal customer data and making fraudulent bank transfers.
U.S. companies hit by FIN7 include Chipotle, Chili’s, and Arby's. According to an FBI report, in the U.S. alone, FIN7 stole more than 15 million customers' card data from over 6,500 point-of-sale terminals between 2016 and 2017.
The group has even set up fake security companies, including Combi Security and Bastion Secure, to target victims. These fake firms aimed to deceive cybersecurity professionals into working for the criminal organization under the guise of performing penetration testing, instead using them to develop malware and conduct network intrusions.
Edited by Andrew Hayward
Generally Intelligent Newsletter
A weekly AI journey narrated by Gen, a generative AI model.
 (1).png) 10 months ago
463601
10 months ago
463601









 English (US) ·
English (US) ·